exploit
An exploit is a code that takes advantage of a software vulnerability or security flaw. It is written either by security researchers as a proof-of-concept threat or by malicious actors for use in their operations. When used, exploits allow an intruder to remotely access a network and gain elevated privileges, or move deeper into the network.
In some cases, an exploit can be used as part of a multi-component attack. Instead of using a malicious file, the exploit may instead drop another malware, which can include backdoor Trojans and spyware that can steal user information from the infected systems. 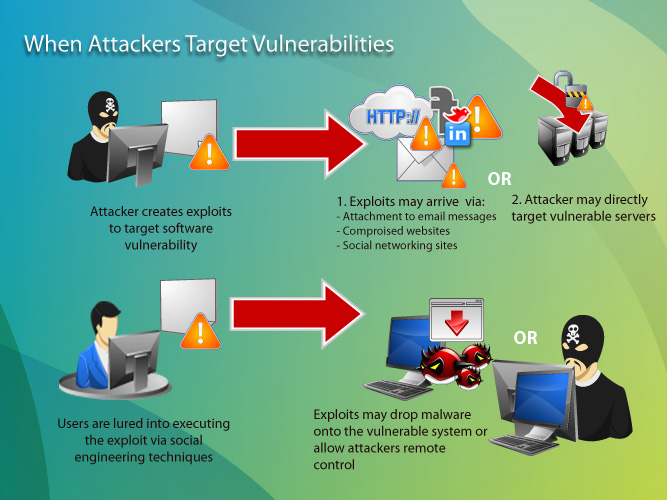
Zero-Day Exploits and Exploit Kits
Based on popular usage of exploit terms, an exploit is referred to as a zero-day exploit when it is used to attack a vulnerability that has been identified but not yet patched, also known as a zero-day vulnerability.
Exploits are often incorporated into malware, allowing them to propagate and run intricate routines on vulnerable computers. Exploit kits are popular in the cybercriminal underground because they provide management consoles, an array of exploits that target different applications, and several add-on functions that make it easier to launch an attack. They were first offered in the Russian underground in 2006.
Evolution of Exploits
2006 and earlier |
|
2007 |
|
2008 |
|
2009 |
|
2010 |
|
2011 |
|
2012 |
|
2013 |
|
2014 |
|
2015 |
|
2016 |
|
?
Mitigating Exploits
Virtual patching is one of the most recommended mitigation solutions for enterprises. Virtual patching works on the premise that exploits take a definable path to and from an application in order to use a software flaw. It is, therefore, possible to create rules at the network layer that can control communication with a target software. By scanning traffic for protocols used, you can, to a certain extent, prevent exploits from doing what they set out to do.?
Related terms:Exploit kit, zero-day exploit, cookies, hacking, vulnerability, virtual patching, SQL injection, cross-side scripting, Internet of Things
Related papers or primers :
Virtual Patching in Mixed Environments: How It Works To Protect YouRelated infographics:
Shellshock Vulnerability: The Basics of the ��Bash Bug��
Dodging a Compromise: A Peek at Exposure Gaps
The Internet of Everything: Layers, Protocols and Possible Attacks
Graphics:
Links :
/vinfo/hk-en/security/news/vulnerabilities-and-exploits/exploit-kits-past-present-and-future