WORM_PALEVO.KK
Windows 98, ME, NT, 2000, XP, Server 2003


Threat Type: Worm
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
Propagates via removable drives, Propagates via peer-to-peer networks, Propagates via instant messaging applications
This malware has received attention from independent media sources and/or other security firms.
To get a one-glance comprehensive view of the behavior of this Worm, refer to the Threat Diagram shown below.

This worm is also capable of performing denial of service (DoS) attacks on target systems. It receives commands from a remote server that is controlled by a malicious user to perform SYN flood attacks against target systems.
It also receives commands from the remote server to perform other actions, such as downloading other malware and downloading updates of itself.
This worm arrives via removable drives. It may be downloaded by other malware/grayware/spyware from remote sites. It may be downloaded by other malware/grayware from remote sites. It may be unknowingly downloaded by a user while visiting malicious websites.
It bears the file icons of certain applications to avoid easy detection and consequent removal.
It creates folders in all physical and removable drives. It drops an AUTORUN.INF file to automatically execute the copies it drops when a user accesses the drives of an affected system.
It runs certain commands that it receives remotely from a malicious user. Doing this puts the affected computer and information found on the computer at greater risk.
TECHNICAL DETAILS
Varies
PE
Yes
03 May 2010
Displays graphics/image, Launches DoS/DDoS attacks, Compromises system security
Arrival Details
This worm arrives via removable drives.
It may be downloaded by other malware/grayware/spyware from remote sites.
It may be downloaded by the following malware/grayware from remote sites:
- SWF_PALEVO.KK
It may be unknowingly downloaded by a user while visiting malicious websites.
It may be unknowingly downloaded by a user while visiting the following malicious websites:
- http://www.{BLOCKED}com.com/FlashPlayer10.0.45.2.exe
Installation
This worm adds the following folders:
- %System Root%\RECYCLER
- %System Root%\RECYCLER\{SID}
(Note: %System Root% is the root folder, which is usually C:\. It is also where the operating system is located.)
It drops the following copies of itself into the affected system:
- %System Root%\RECYCLER\{SID}\recycle.exe
- %User Temp%\setup32temp.exe
(Note: %System Root% is the root folder, which is usually C:\. It is also where the operating system is located.. %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, XP, and Server 2003.)
It drops the following files:
- %System Root%\RECYCLER\{SID}\Desktop.ini
- {drive letter}:\U3ROM\Desktop.ini
(Note: %System Root% is the root folder, which is usually C:\. It is also where the operating system is located.)
It bears the file icons of the following applications:
- Recycle Bin
Autostart Technique
This worm adds the following registry entries to enable its automatic execution at every system startup:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Winlogon
Taskman = "%System Root%\RECYCLER\{SID}\recycle.exe"
Propagation
This worm creates the following folders in all physical and removable drives:
- {drive letter}:\U3ROM
It drops copies of itself into the following folders used in peer-to-peer (P2P) networks:
- Ares
- BearShar
- iMesh
- Shareaza
- Kazaa
- DC++
- eMule
- LimeWire
It drops the following copy(ies) of itself in all removable drives:
- {drive letter}:\U3ROM\flyhigh.exe
It drops an AUTORUN.INF file to automatically execute the copies it drops when a user accesses the drives of an affected system.
The said .INF file contains the following strings:
;{garbage characters}
[AutoRun
;{garbage characters}
open=U3ROM/flyhigh.exe
;{garbage characters}
:jmp0
;{garbage characters}
icon=%System%\SHELL32.dll,4
;{garbage characters}
:jmp3
;{garbage characters}
action=Open folder to view files using Windows Explorer
;{garbage characters}
shelL\opeN\commanD=U3ROM/flyhigh.exe
;{garbage characters}
Shell\Explore\Command=U3ROM/flyhigh.exe
;{garbage characters}
useautoplay=1
;{garbage characters}
:GOTO NUL
(Note: %System% is the Windows system folder, which is usually C:\Windows\System on Windows 98 and ME, C:\WINNT\System32 on Windows NT and 2000, or C:\Windows\System32 on Windows XP and Server 2003.)
It sends the following messages using the aforementioned Instant Messaging applications:
MSN Messenger
Backdoor Routine
This worm executes the following command(s) from a remote malicious user:
- Download other malware
- Update itself
- Launch Denial of Service (DoS) attacks against target systems
Other Details
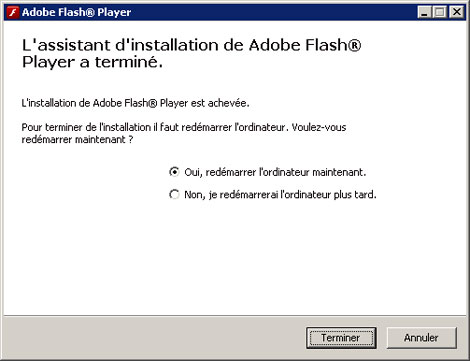
This worm displays the following images:
SOLUTION
8.900
7.151.00
07 May 2010
Step 1
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you to allow full scanning of your computer.
Step 2
Remove the malware/grayware file that dropped/downloaded WORM_PALEVO.KK