Ransomware Recap: SnakeLocker Hides Under Two Names
 Ransomware operators continue to diversify their attack tactics with the discovery of SnakeLocker—a new variant that uses two names in an attempt to dodge security scanners.
Ransomware operators continue to diversify their attack tactics with the discovery of SnakeLocker—a new variant that uses two names in an attempt to dodge security scanners.
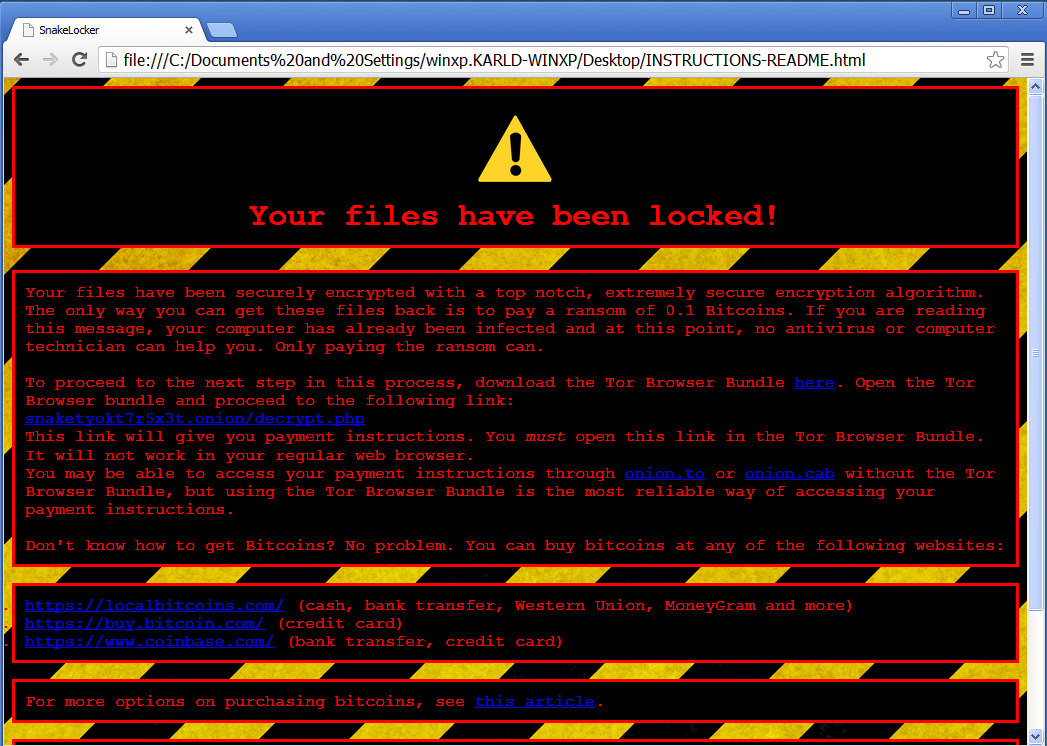
Figure 1. SnakeLocker ransom note
In its ransom note, SnakeLocker poses as an accommodating file hostage-taker by politely outlining instructions to victims who may not know how to purchase Bitcoins (BTC). It demands victims to pay a ransom of 0.1 BTC to get their files back.
Here are other notable ransomware stories this week:
Bam
The Bam ransomware (Ransom_BAM.A) claims to have used a special crypto-code to encrypt the victims’ files. Its lock screen doesn’t mention any ransom amount, but it instructs the victim to contact the indicated email addresses to buy the needed decrypt tool.
 Figure 2. Bam ransom note
Figure 2. Bam ransom note
When executed, Bam appends encrypted files with a .bam extension name and targets a large number of file types that include font, programming, database, word processor, and text file formats.
Symbiom
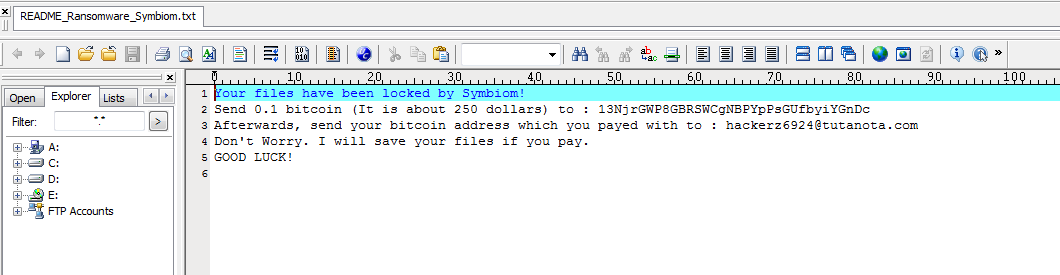
Figure 3. Symbiom ransom note
Meanwhile, run-of-the-mill ransomware variants still exist with the discovery of Symbiom (Ransom_CRYPTEARSYMB.A). This new variant adds ‘symbiom_ransomware_locked’ to the files it encrypt. It encrypts a variety of file types that include Microsoft Office documents, as well as video, audio, and image file formats, and demands a ransom of 0.1 Bitcoin (US$250) to decrypt the files.
Users and security administrators in organizations should stay vigilant against the diversifying threats of ransomware. Regularly ?important files can mitigate the damage caused by a ransomware infection, but a?multi-layered approach?is key to defending all possible gateways from ransomware.
Ransomware Solutions
Enterprises can benefit from a multi-layered, step-by-step approach in order to best mitigate the risks brought by these threats. Email and web gateway solutions such as?live casino online? Deep Discovery? Email Inspector?and?InterScan? Web Security?prevent ransomware from ever reaching end users. At the endpoint level,?live casino online Smart Protection Suites?deliver several capabilities like high-fidelity machine learning, behavior monitoring and application control, and vulnerability shielding that minimizes the impact of this threat.?live casino online Deep Discovery Inspector?detects and blocks ransomware on networks, while?live casino online Deep Security??stops ransomware from reaching enterprise servers–whether physical, virtual or in the cloud.?
For small businesses,?live casino online Worry-Free Services Advanced?offers cloud-based email gateway security through Hosted Email Security. Its endpoint protection also delivers several capabilities such as behavior monitoring and real-time web reputation in order detect and block ransomware.?
For home users,?live casino online Security 10?provides strong protection against ransomware by blocking malicious websites, emails, and files associated with this threat.?
End users and enterprises can also benefit from multilayered mobile security solutions such as ? ? (available on ), and ? for Apple devices (available on the ). ? provide device, compliance and application management, data protection, and configuration provisioning, as well as protect devices from attacks that leverage vulnerabilities, preventing unauthorized access to apps, as well as detecting and blocking malware and fraudulent websites.?
Users can likewise take advantage of our?free tools?such as the?, which is designed to detect and remove screen-locker ransomware; as well as?, which can decrypt certain variants of crypto-ransomware without paying the ransom or the use of the decryption key.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- Unveiling AI Agent Vulnerabilities: Code Execution
- Unveiling AI Agent Vulnerabilities Part I: Introduction to AI Agent Vulnerabilities
- The Ever-Evolving Threat of the Russian-Speaking Cybercriminal Underground
- From Registries to Private Networks: Threat Scenarios Putting Organizations in Jeopardy
- Trend 2025 Cyber Risk Report
 Cellular IoT Vulnerabilities: Another Door to Cellular Networks
Cellular IoT Vulnerabilities: Another Door to Cellular Networks AI in the Crosshairs: Understanding and Detecting Attacks on AWS AI Services with Trend Vision One?
AI in the Crosshairs: Understanding and Detecting Attacks on AWS AI Services with Trend Vision One? Trend 2025 Cyber Risk Report
Trend 2025 Cyber Risk Report CES 2025: A Comprehensive Look at AI Digital Assistants and Their Security Risks
CES 2025: A Comprehensive Look at AI Digital Assistants and Their Security Risks