Backdoor.PHP.DEWMODE.A
Windows

Threat Type:
Backdoor
Destructiveness:
No
Encrypted:
No
In the wild::
Yes
OVERVIEW
It arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites. Este malware podr��a introducirse utilizando uno o varios m��todos de entrada.
Ejecuta comandos desde un usuario remoto malicioso que pone en peligro el sistema afectado.
TECHNICAL DETAILS
Detalles de entrada
It arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Entra a trav��s de los siguientes medios:
- It may be delivered by exploiting the following vulnerabilities:
- CVE-2021-27101
- CVE-2021-27102
- CVE-2021-27103
- CVE-2021-27104
Rutina de puerta trasera
Ejecuta los comandos siguientes desde un usuario remoto malicioso:
- Download files from victim server
- Delete traces in the system
Rutina de infiltraci��n
Infiltra los archivos siguientes:
- /tmp/.scr �� temporary file used to delete traces of the malware when requested by the C&C; deleted afterwards.
- /tmp/.out �� temporary file used to redirect logging of malware trace deletion; deleted afterwards.
Otros detalles
Hace lo siguiente:
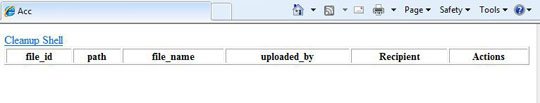
- Once accessed, it will display the list of files existing in the SQL database hosted in the target server
- It displays the following if no files are present in the database:
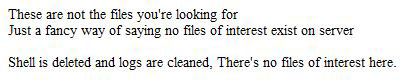
- It uses the dropped file /tmp/.scr to delete traces of itself in the server. This dropped file does the following:
- Remove the line referencing the malware in all of the logs located in "/var/opt/apache".
- Overwrite the contents of adminpl.log with blanks.
- Delete malware trace in the machine.
- Overwrite /var/log/secure with blanks.
SOLUTION
Step 1
Los usuarios de Windows ME y XP, antes de llevar a cabo cualquier exploraci��n, deben comprobar que tienen desactivada la opci��n Restaurar sistema para permitir la exploraci��n completa del equipo.
Step 2
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 3
Explorar el equipo con su producto de live casino online para eliminar los archivos detectados como Backdoor.PHP.DEWMODE.A En caso de que el producto de live casino online ya haya limpiado, eliminado o puesto en cuarentena los archivos detectados, no ser��n necesarios m��s pasos. Puede optar simplemente por eliminar los archivos en cuarentena. Consulte esta para obtener m��s informaci��n.
Did this description help? Tell us how we did.

