Backdoor.PHP.WEBSHELL.AC
Windows, Linux

Tipo de malware
Backdoor
Destructivo?
No
Cifrado
No
In the Wild:
����
Resumen y descripci��n
It arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Este malware no tiene ninguna rutina de propagaci��n.
Ejecuta comandos desde un usuario remoto malicioso que pone en peligro el sistema afectado.
Detalles t��cnicos
Detalles de entrada
It arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
�ʰ��DZ貹������������
Este malware no tiene ninguna rutina de propagaci��n.
Rutina de puerta trasera
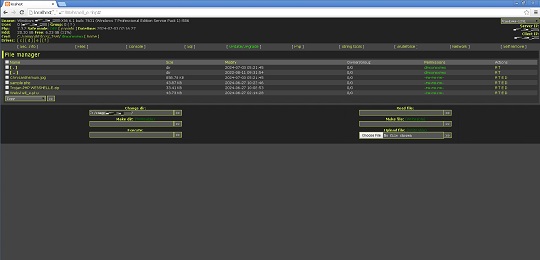
Ejecuta los comandos siguientes desde un usuario remoto malicioso:
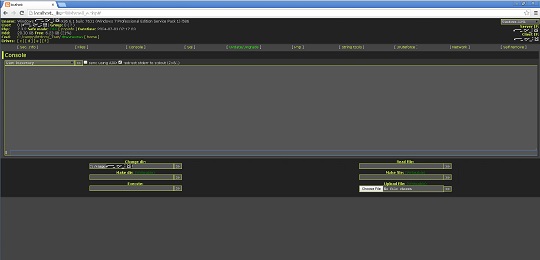
- Execute cmd commands
- Create directories
- Create file
- Execute files
- View file
- Edit file
- Rename file
- Upload file
- Download file
- Delete file
- Change file permission
- Change file attributes
- Change last modify time of files
- Search files
- Search hash
- Delete itself
Robo de informaci��n
Recopila los siguientes datos:
- Computer name
- Operating system
- User name
- Group name
- PHP version
- Date and Time
- Computer mode (Safe Mode on or off)
- Client IP address
- Server IP address
- Current working directory
- Hard drive total space
- Hard drive free space
- Disk drives present
- Server software
- Loaded Apache modules
- Disabled PHP Functions
- cURL support
- OS version
- User accounts
- Directories of the following (For Linux):
- Open_basedir
- Safe_mode_exec_dir
- Safe_mode_include_dir
- Complete file directory for all disk drives including:
- File Name
- File size
- Last modified date
- Owners/Group
- File Permissions
- Active connections in infected machine
- Running Windows services in infected machine
- User accounts in infected machine
- Connected computers in the infected machine
- ARP Table of the infected machine
- IP Configuration of the infected machine
Otros detalles
Hace lo siguiente:
- It can access SQL and PostgreSQL database (requires Host, Username, Password, and Database name )
- It connects to the following URL to acquire an update:
- http://{BLOCKED}ack.live/96382367f90798e98d30f82012963197.htm
However, as of this writing, the said site is inaccessible.
- Execute PHP code using 'eval' function
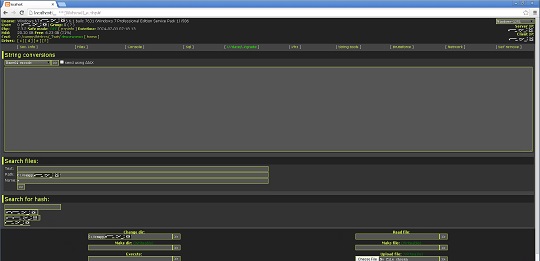
- Contains a collection of string tools:
- Base64 encoding/decoding
- URL encoding/decoding
- Full URL encoding
- Generate MD5 hash
- Generate SHA1 hash
- Generate CRYPT hash
- Generate CRC32 hash
- Generate HTML formatted special characters
- Convert ASCII to hexadecimal
- Convert hexadecimal to ASCII
- Convert hexadecimal to decimal
- Convert hexadecimal to binary
- Convert decimal to hexadecimal
- Convert decimal to binary
- Convert binary to hexadecimal
- Convert binary to decimal
- Convert lower case string to upper case string and vice versa
- Calculate string length
- Search for hash using the following URLs:
- https://hashcracking.ru/index.php
- http://md5.rednoize.com/
- http://{BLOCKED}or.me/index.php
However, as of this writing, the said sites are inacessible.
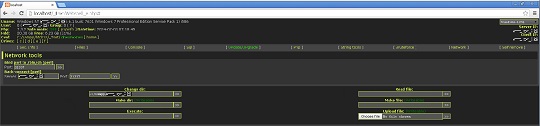
- Conduct brute force attack on FTP, MySQL, and PostgreSQL servers
- Conduct back connection for PERL and PHP threads (requires IP address and port number)
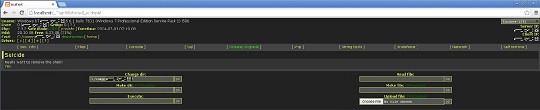
- It displays the following GUI:


Soluciones
Step 1
Los usuarios de Windows ME y XP, antes de llevar a cabo cualquier exploraci��n, deben comprobar que tienen desactivada la opci��n Restaurar sistema para permitir la exploraci��n completa del equipo.
Step 2
Explorar el equipo con su producto de live casino online para eliminar los archivos detectados como Backdoor.PHP.WEBSHELL.AC En caso de que el producto de live casino online ya haya limpiado, eliminado o puesto en cuarentena los archivos detectados, no ser��n necesarios m��s pasos. Puede optar simplemente por eliminar los archivos en cuarentena. Consulte esta para obtener m��s informaci��n.
Rellene nuestra encuesta!


