Backdoor.PHP.WEBSHELL.AC
Windows, Linux

Malware-Typ:
Backdoor
Zerstrerisch?:
Nein
Verschlsselt?:
Nein
In the wild::
Ja
?berblick
It arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Diese Malware hat keine Verbreitungsroutine.
F��hrt Befehle eines externen, b?swilligen Benutzers aus, wodurch das betroffene System gef?hrdet wird.
Technische Details
?bertragungsdetails
It arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Verbreitung
Diese Malware hat keine Verbreitungsroutine.
Backdoor-Routine
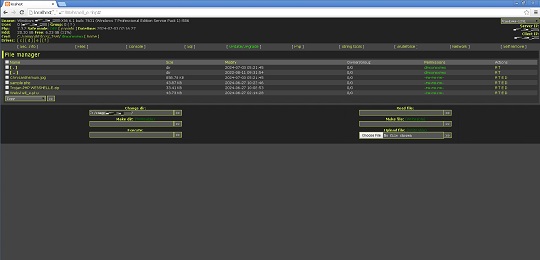
F��hrt die folgenden Befehle eines externen, b?swilligen Benutzers aus:
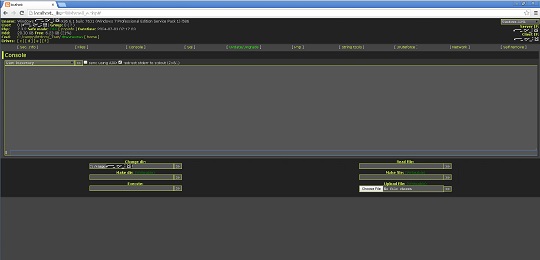
- Execute cmd commands
- Create directories
- Create file
- Execute files
- View file
- Edit file
- Rename file
- Upload file
- Download file
- Delete file
- Change file permission
- Change file attributes
- Change last modify time of files
- Search files
- Search hash
- Delete itself
Datendiebstahl
Folgende Daten werden gesammelt:
- Computer name
- Operating system
- User name
- Group name
- PHP version
- Date and Time
- Computer mode (Safe Mode on or off)
- Client IP address
- Server IP address
- Current working directory
- Hard drive total space
- Hard drive free space
- Disk drives present
- Server software
- Loaded Apache modules
- Disabled PHP Functions
- cURL support
- OS version
- User accounts
- Directories of the following (For Linux):
- Open_basedir
- Safe_mode_exec_dir
- Safe_mode_include_dir
- Complete file directory for all disk drives including:
- File Name
- File size
- Last modified date
- Owners/Group
- File Permissions
- Active connections in infected machine
- Running Windows services in infected machine
- User accounts in infected machine
- Connected computers in the infected machine
- ARP Table of the infected machine
- IP Configuration of the infected machine
Andere Details
Es macht Folgendes:
- It can access SQL and PostgreSQL database (requires Host, Username, Password, and Database name )
- It connects to the following URL to acquire an update:
- http://{BLOCKED}ack.live/96382367f90798e98d30f82012963197.htm
However, as of this writing, the said site is inaccessible.
- Execute PHP code using 'eval' function
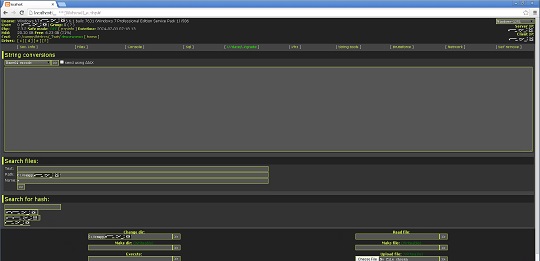
- Contains a collection of string tools:
- Base64 encoding/decoding
- URL encoding/decoding
- Full URL encoding
- Generate MD5 hash
- Generate SHA1 hash
- Generate CRYPT hash
- Generate CRC32 hash
- Generate HTML formatted special characters
- Convert ASCII to hexadecimal
- Convert hexadecimal to ASCII
- Convert hexadecimal to decimal
- Convert hexadecimal to binary
- Convert decimal to hexadecimal
- Convert decimal to binary
- Convert binary to hexadecimal
- Convert binary to decimal
- Convert lower case string to upper case string and vice versa
- Calculate string length
- Search for hash using the following URLs:
- https://hashcracking.ru/index.php
- http://md5.rednoize.com/
- http://{BLOCKED}or.me/index.php
However, as of this writing, the said sites are inacessible.
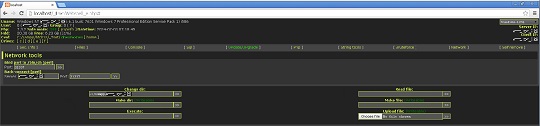
- Conduct brute force attack on FTP, MySQL, and PostgreSQL servers
- Conduct back connection for PERL and PHP threads (requires IP address and port number)
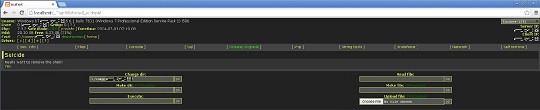
- It displays the following GUI:


L?sungen
Step 1
F��r Windows ME und XP Benutzer: Stellen Sie vor einer Suche sicher, dass die Systemwiederherstellung deaktiviert ist, damit der gesamte Computer durchsucht werden kann.
Step 2
Durchsuchen Sie Ihren Computer mit Ihrem live casino online Produkt, und l?schen Sie Dateien, die als Backdoor.PHP.WEBSHELL.AC entdeckt werden. Falls die entdeckten Dateien bereits von Ihrem live casino online Produkt ges?ubert, gel?scht oder in Quarant?ne verschoben wurden, sind keine weiteren Schritte erforderlich. Dateien in Quarant?ne k?nnen einfach gel?scht werden. Auf dieser finden Sie weitere Informationen.
Nehmen Sie an unserer Umfrage teil


